Blog
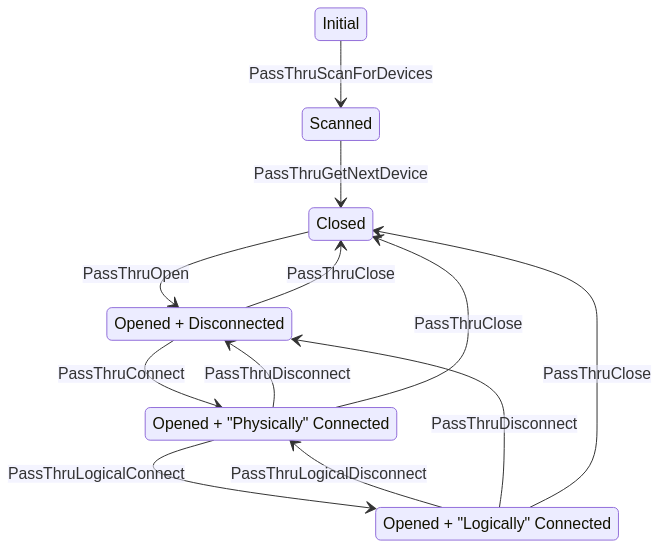
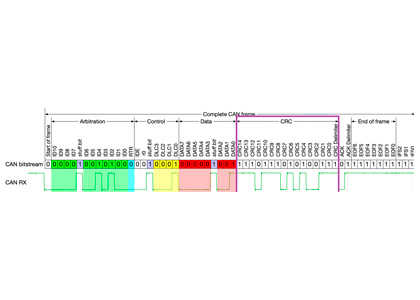
How CRC is generated in a CAN bus frame?
Brent Johnny
08/09/2023
Generating Cyclic Redundancy Checks (CRC) in Controller...
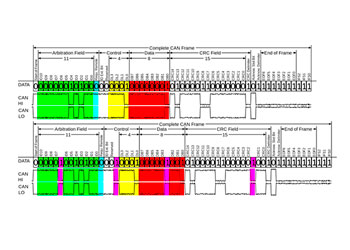
Understanding Bit Stuffing in CAN Bus Systems
Will Caruana
07/20/2023
IntroductionThe Controller Area Network (CAN) bus is...
Is Europe ready to say Good-Bye to fuel powered vehicles?
Irene Canas
07/10/2023
In February, the European parliament voted to...
ASRG Amsterdam Meetup: Hack a car. Vehicle Penetration Testing with real cars
Robert Leale
07/10/2023
Details ASRG Amsterdam Meetup: Hack a car....
Anomaly Detection and Analysis for Vehicle CANbus Data
Robert Leale
06/30/2023
Introducing Canbana: Unlocking Anomaly Detection and Analysis...