Blog
Using password attacks to gain SSH access to car infotainment systems
Arnold
04/02/2024
In the evolving landscape of automotive technology,...
ASRG Amsterdam Meetup: Hack a car. Vehicle Penetration Testing with real cars – 12 July 2024
Emmanuel Cabrera
02/21/2024
Details ASRG Amsterdam Meetup: Hack a car....
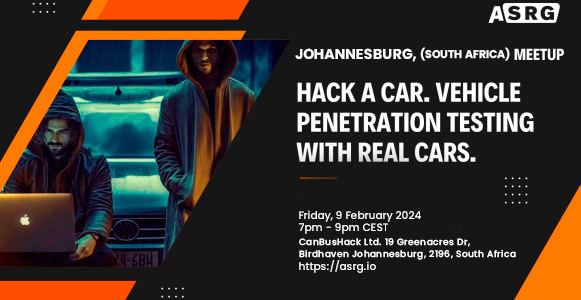
ASRG Johannesburg, South Africa Meetup: Hack a car. Penetration Testing with real cars – 9 Feb 2024
Emmanuel Cabrera
02/01/2024
Details ASRG Johannesburg, South Africa Meetup: Hack...
UNIFIED DIAGNOSTIC SERVICE (UDS) Service: 0x22 – Read Data by Identifier
Brent Johnny
01/25/2024
In this post we’re going to take...
Schedule a meeting with us at CES 2024 – Las Vegas, NV
Emmanuel Cabrera
01/07/2024
Request a Meeting >