Blog
AI and Automotive Cypher Security
Zein Khaddour
12/11/2023
AI has the potential to significantly impact...
Revolutionizing Vehicle Telematics with the CANBusHack Data Logger
Robert Leale
12/04/2023
In today's world, vehicle telematics plays a...
Vehicle Immobilizers: Harnessing the Power of CAN Bus Integration with CanBusHack
Robert Leale
11/27/2023
In today's world, vehicle security has transcended...
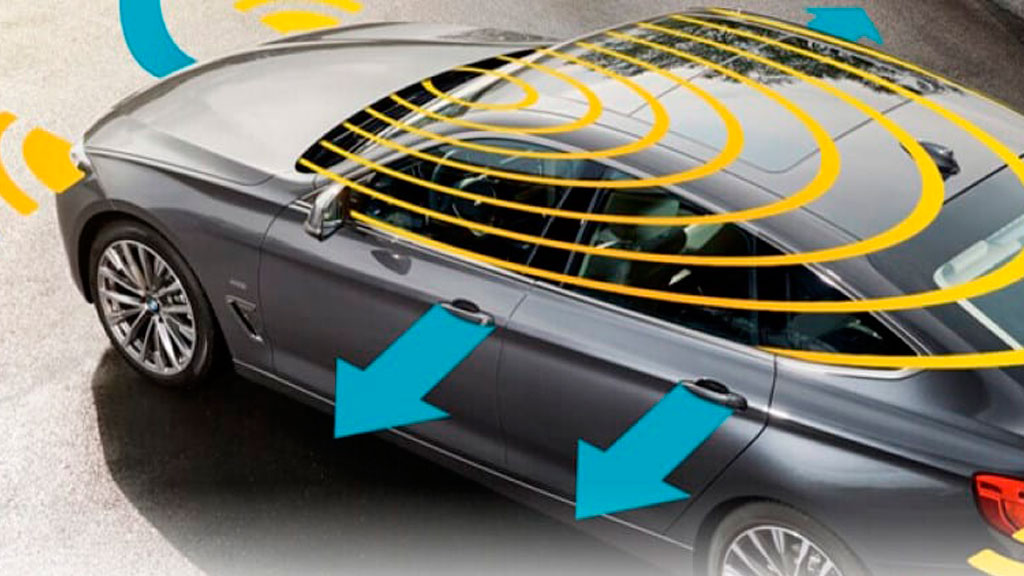
Integrating Vehicle Alarm Systems with the CAN Bus Network: Functionality and Challenges
Robert Leale
11/21/2023
In the ever-evolving landscape of automotive technology,...
Revolutionizing Mining Telematics with the CANBusHack Data Logger
Robert Leale
11/16/2023
Mining telematics plays a crucial role in...